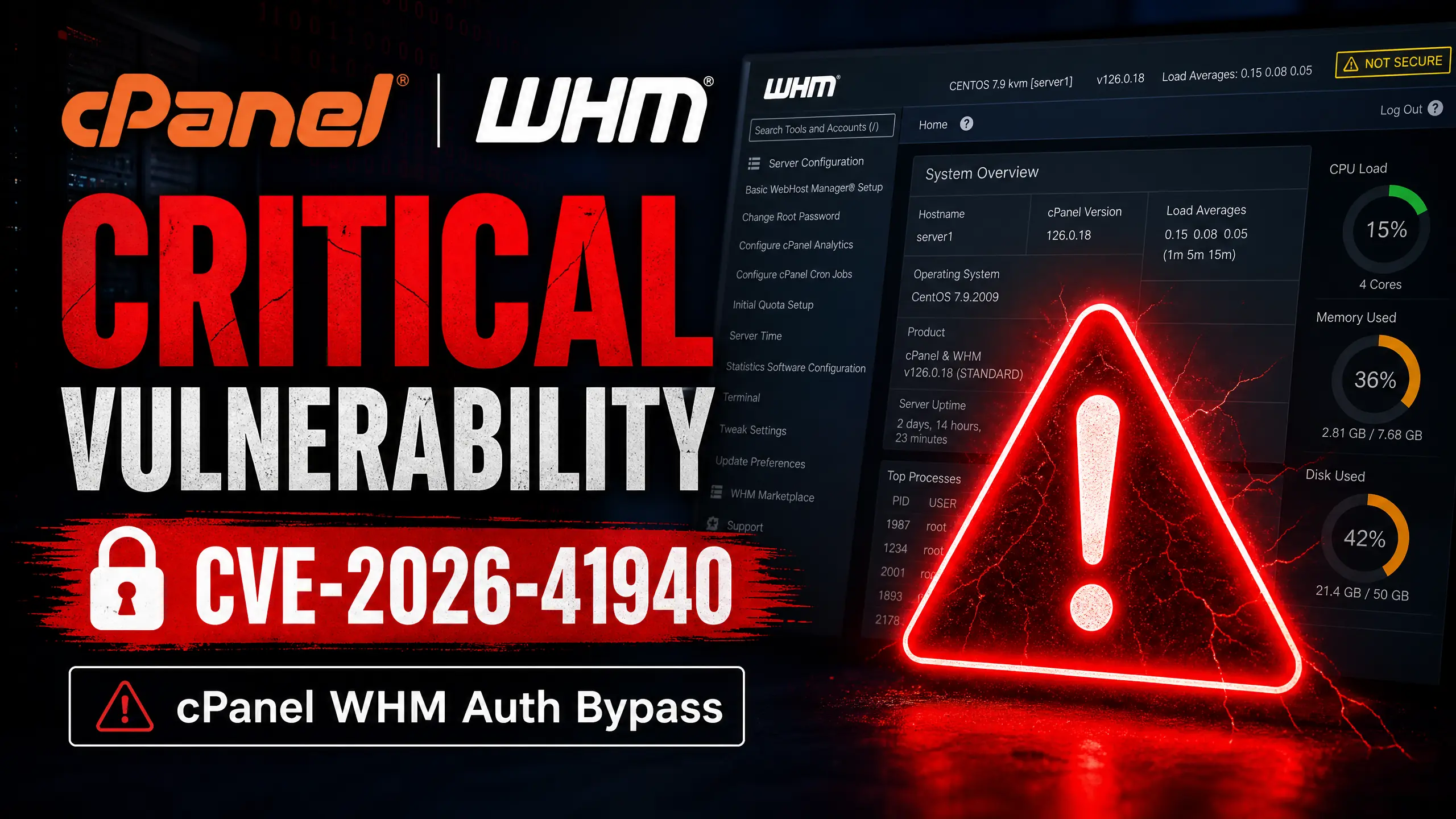
CVE-2026-41940: Critical cPanel & WHM Auth Bypass Explained

Malik Farooq
May 3, 2026

Deep Dive
CVE-2026-41940: Critical cPanel & WHM Auth Bypass Explained
Introduction: A CVSS 9.8 Threat Hitting Millions of Servers
On April 28, 2026, cPanel published a security advisory that sent the hosting industry into emergency mode. CVE-2026-41940 — a CVSS 9.8 critical authentication bypass — allows an unauthenticated attacker to gain full administrative access to servers running cPanel & WHM. Every supported version is affected.
If you manage a cPanel server and have not patched yet, this is your highest priority action item today.
How the Attack Works: CRLF Injection on the Session Cookie
The vulnerability chains three separate flaws to achieve a complete authentication bypass:
Flaw 1: Truncated Cookie and Loss of Encryption
The
whostmgrsessionFlaw 2: No Sanitization of Newline Characters
The WHM session handler does not sanitize CRLF (
\r\nFlaw 3: Bypassing Password Validation
By combining the above two flaws, an attacker can craft a request that the server treats as an authenticated WHM root session — without ever providing a password.
Affected and Patched Versions
| Status | Versions |
|---|---|
| Vulnerable | All supported cPanel & WHM releases before the April 28 patch |
| Patched | cPanel v114+, v118+, v120+ (emergency update released April 28) |
What to Do Now: Operational Guide
1. Force the Update Immediately
/scripts/upcp --force
This pulls the latest patched build. Verify with:
/usr/local/cpanel/cpanel -V
2. Temporary Mitigation (If Update is Delayed)
Block WHM port (2087) at the firewall for all non-admin IPs:
# Using CSF (ConfigServer Security & Firewall) csf -d [external_ip] "Blocking WHM access during CVE-2026-41940 mitigation"
3. Forensic Audit: Check If You've Already Been Compromised
Review WHM access logs for anomalous root sessions before April 28:
grep "ROOT" /usr/local/cpanel/logs/access_log | grep -v "127.0.0.1"
Look for sessions from unexpected IPs, especially with session tokens that look malformed or truncated.
If You're on Shared Hosting (No Root Access)
Contact your hosting provider immediately. Ask them to confirm:
- Which cPanel version they are running.
- Whether they have applied the April 28 emergency patch.
- Whether they are blocking external WHM access at the network level.
Conceptual Representation

In Practice

Conclusion
CVE-2026-41940 is one of the most severe hosting vulnerabilities in recent years. The CRLF injection chain is elegant and requires no credentials — making it trivially automatable. If you run cPanel, patch now. If you host clients on cPanel, notify them and document your remediation.
References
[1] cPanel Security Advisory, April 28, 2026.
[2] NIST CVE-2026-41940 Entry, National Vulnerability Database.
[3] Cybersecurity Trends Analysis, SecureCode Institute, 2026.
[4] Original Article: https://pasqualepillitteri.it/en/news/1608/cve-2026-41940-cpanel-whm-authentication-bypass-en
Ready to master AI?
Join 1,000+ professionals getting the edge in AI marketing. 3 minutes a day to 10x your growth.
Join Free NowKeep reading

Meta Ads MCP for Claude
Learn the latest AI strategies to stay ahead in the marketing game.
Malik Farooq/

NotebookLM April 2026: Mobile, Cinematic Video & Gemini Sync
Learn the latest AI strategies to stay ahead in the marketing game.
Malik Farooq/

NotebookLM April 2026 Update
Learn the latest AI strategies to stay ahead in the marketing game.
Malik Farooq/
Back to archive
Share